The 7 Best Browsers for Privacy & Anonymity
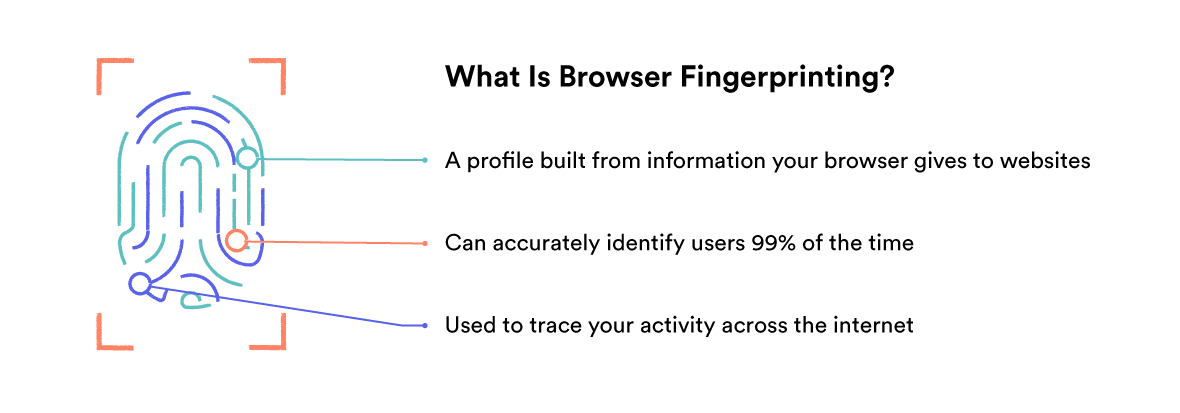
Using the best private browser can go a long way in protecting you from online tracking, WebRTC leaks, and browser fingerprinting.
There isn’t a single best privacy browser, though, because privacy needs and preferences will differ between users.
All the private browsers we recommend here are open-source. They offer minimal-reliance on big tech companies, custom settings, and active protection against online tracking.
1. Mozilla Firefox: Best ‘Mainstream’ Private Browser
![]()
- The most private mainstream browser available in 2024
- Includes protection against third party trackers
- Completely open-source
- Receives frequent security updates
- Needs some configuration for optimal privacy
Once configured properly, the Firefox browser is the best private browser available in terms of performance, ease-of-use, and privacy.
You can read the Firefox privacy policy here.
Firefox has two great advantages. The first is that it is completely open-source. The second is that it is highly customizable.
Because it is open-source, Firefox forms the basis for lots of other privacy-focused browsers. You can also inspect the code to make sure Mozilla is honest about the way the browser behaves.
Unlike Chrome, Opera, or Microsoft Edge, Firefox lets you customize its privacy settings to exclude all telemetry (sending data back to Mozilla) and third-party add-ons.
This means even the standard version of Firefox is a potentially great private browser.
In the past, we’ve seen some VPN extensions suffer WebRTC leaks in Firefox. See how to solve this further down the page. Or, use one of the VPNs we recommend for Firefox..
How to Optimize Firefox for Privacy
The most important thing to remember when using the basic version of Firefox is that you optimize your settings for privacy.
The first and most important change you need to make when optimizing Firefox for privacy is to disable telemetry – the setting which allows your browser to send technical data back to Mozilla.
Firefox has an interactive development process which uses feedback from users and includes experimental builds like Firefox Nightly and Firefox Developer Edition. These are great if you want to help contribute to Firefox’s development, but they aren’t private.
To disable telemetry in Firefox:
- Select the preferences or settings menu in the top right hand corner of your screen.
- Navigate to Preferences > Privacy & Security > Firefox Data Collection and Use.
- Uncheck every box in this section.

How to disable Telemetry in Firefox.
Firefox also has a feature which can block trackers, cookies, fingerprinters and cryptominers, called Enhanced Tracking Protection.
To enable Enhanced Tracking Protection in Firefox:
- Select the settings menu in the top right hand corner of your screen.
- Navigate to Preferences > Privacy & Security > Enhanced Tracking Protection.
- Choose your protection mode: strict, standard, or custom.
In our experience the ‘strict’ mode will break some webpages, but is generally quite stable.
How to enable tracking protection in Firefox.
If you encounter a problem, you can always disable content blocking for specific sites by pressing the “shield” symbol to the left of the URL bar.
You can also change your default search engine from Google to a more private alternative.
To change your default search engine:
- Select the settings menu in the top right hand corner of your screen.
- Navigate to Preferences > Search > Default Search Engine.
- Choose your preferred search engine from the drop-down menu.
Advanced Firefox Privacy Settings
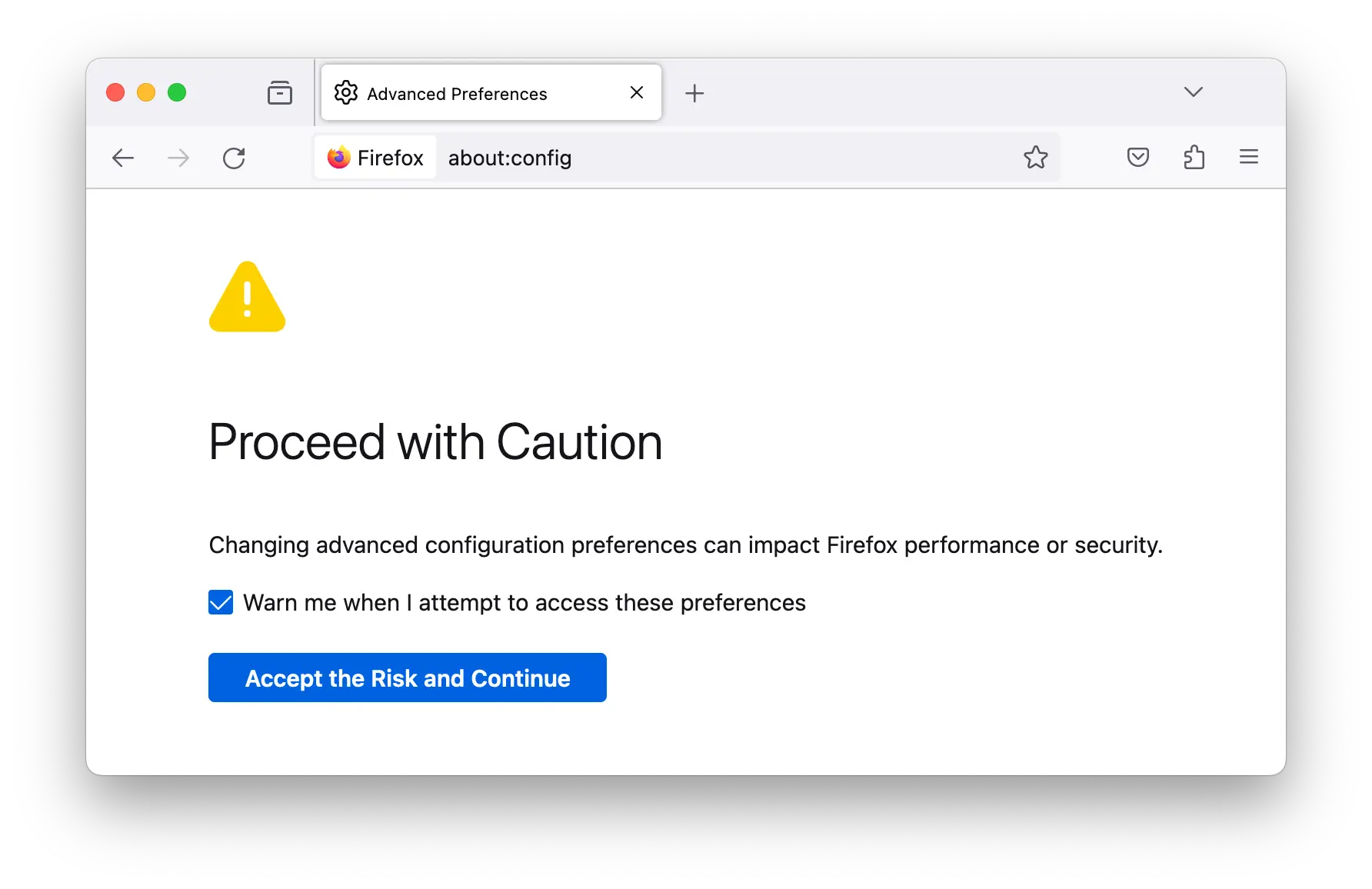
Finally, there are some important advanced settings that can be accessed in Firefox’s advanced preferences menu.
To change these settings, just type about:config into your address bar. Press enter and then click “Accept the risk and continue“. This will take you to the Firefox browser’s advanced configuration menu.
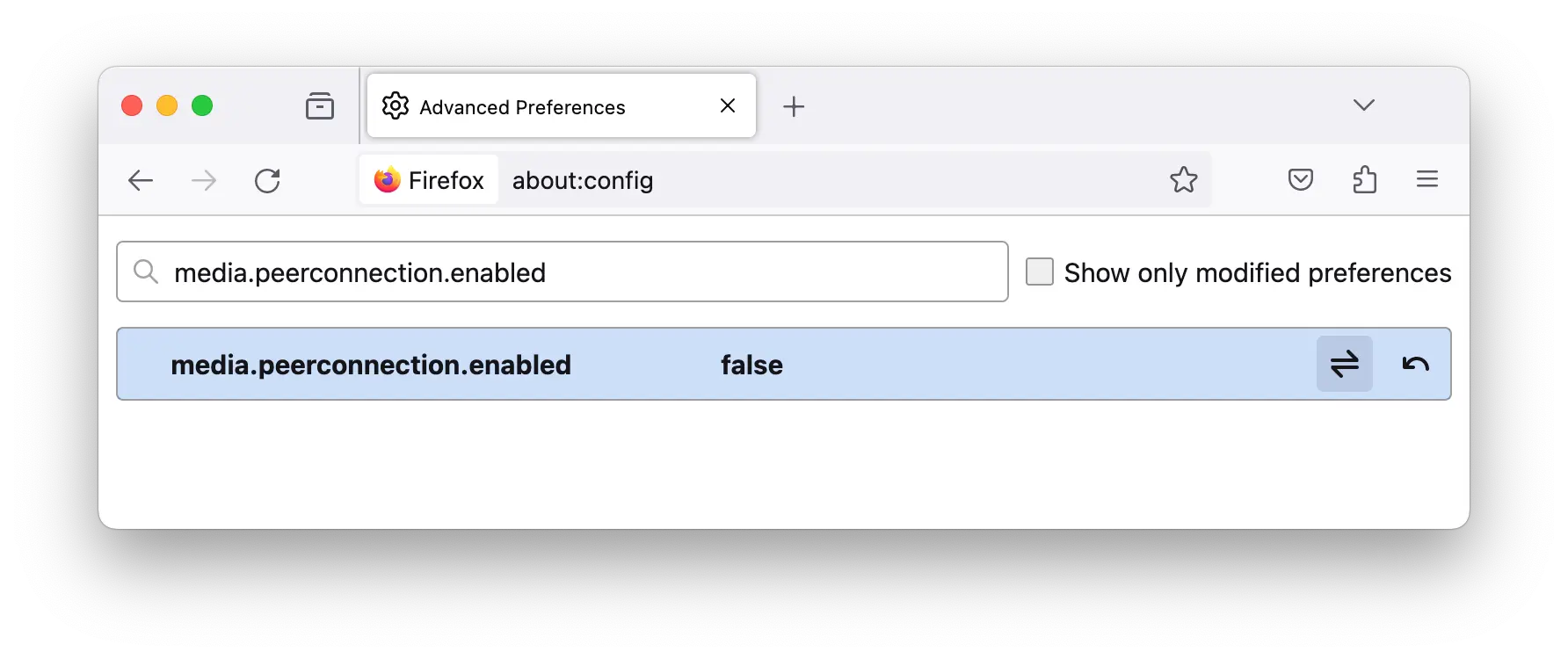
Search for the name of the preference you’d like to change and simply double-click on it to change from true to false or vice versa. This will enable or disable the specific setting.
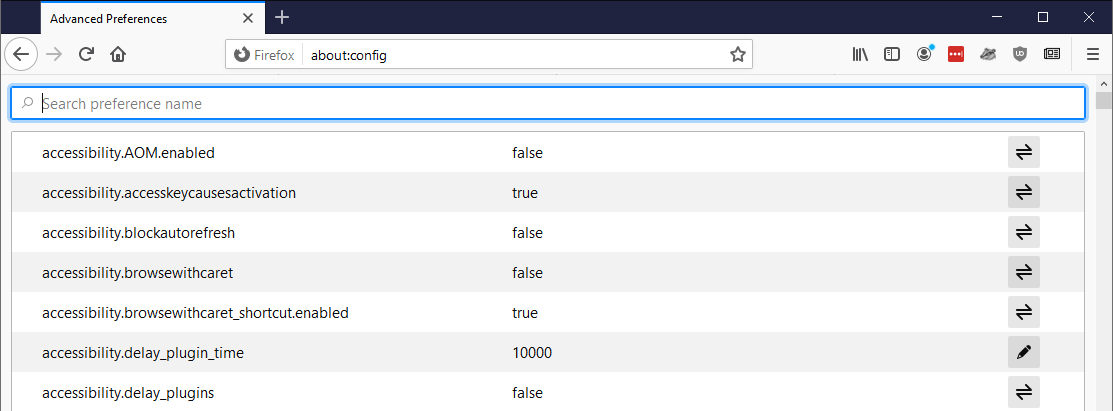
Firefox’s advanced configuration menu.
Here is a list of the most important advanced Firefox privacy settings, and whether it should be enabled for disabled for maximum privacy:
| Preference Name | Set To | Effect |
|---|---|---|
| media.peerconnection.enabled | FALSE |
Disables WebRTC — a real-time communication protocol that can leak your true IP address. |
| privacy.resistFingerprinting | TRUE |
Enables Firefox’s native fingerprint protection. |
| privacy.trackingprotection.fingerprinting.enabled | TRUE |
Enables additional fingerprint protection. |
| privacy.trackingprotection.cryptomining.enabled | TRUE |
Provides extra protection against cryptominers. |
| privacy.firstparty.isolate | TRUE |
Enables first-party isolation. This means cookies, cache, and much more are prevented from tracking you across multiple domains. |
| privacy.trackingprotection.enabled | TRUE |
Enables a filter list to block known third-party trackers. |
| geo.enabled | FALSE |
Firefox uses Google Location Services to find your location. In the process, it sends it your IP address, client identifier, and information about nearby WiFi networks. You can turn this off entirely by selecting false. |
| media.navigator.enabled | FALSE |
Prevents websites from tracking information about your camera and microphone, which is used in fingerprinting. |
| network.cookie.cookieBehaviour | 4 |
This setting runs from 0 to 4 and controls the browser’s cookie policy. Setting it to 0 would allow all cookies. The highest level of protection, 4, enables New Cookie Jar. |
| network.cookie.lifetimePolicy | 2 |
This setting controls how long cookies are stored. Set this to 2 to delete cookies at the end of each session. |
| network.dns.disablePrefetch | TRUE |
Prevents Firefox from prefetching DNS. Prefetching DNS can speed up load times but has some small privacy risks. |
| network.prefetch-next | FALSE |
Prevents Firefox from prefetching pages it thinks you may visit. This has similar privacy risks to prefetching DNS. |
| webgl.disabled | TRUE |
Disables WebGL. WebGL can be used in advanced browser fingerprinting techniques, and also represents a potential security risk. |
| dom.event.clipboardevents.enabled | FALSE |
Prevents websites from knowing when you copy, cut, or paste content. |
| media.eme.enabled | FALSE |
Disables DRM-controlled HTML5 content. |
It’s important not to confuse Mozilla Firefox with Mozilla VPN – a true independent VPN released by the company behind the browser and currently being rolled out worldwide. It is not a browser, and does not even have an extension for Firefox. We were impressed by it in our Mozilla VPN review, though.
2. Firefox Focus: Best Private Mobile Browser

- Stripped-down mobile browser
- Fast without demanding much from your processor
- Includes advanced security options
- Clears cookies and history after each session
Mozilla has been working on its mobile Firefox apps for a while now, and Firefox Focus is the result. Firefox Focus is tailored towards ad-blocking and tracking prevention by default. It’s also really easy to use.
You’ll find a comprehensive set of privacy options including the ability to block trackers of different kinds, block fonts, disable JavaScript, and even customize what kind of cookies are blocked.
The app can be set to block screenshots and obscure your browser’s contents when you switch between tabs. You can even set it to unlock with your fingerprint.
If you want to delete the history and cookies from your current session you simply press a trash-can symbol at the bottom of the page.
Firefox Focus only lets you have one tab open at a time, which means the browsing experience is quite different from what you may be used to. Because it is so stripped down, Focus also allows for a very fast browsing experience.
Overall, Firefox Focus offers a focused experience with great privacy — but you may not want to use it all of the time.
How to Optimize Firefox Focus for Privacy
Firefox Focus has telemetry turned on by default. You should navigate straight to the settings to turn it off.
While you’re there, customize the level of privacy to your preferences. As you’ll find with any super-private browser, turning all of the protections on has a habit of breaking some websites or making them display strangely.
3. LibreWolf: A Reliable Firefox Alternative

- Based on Firefox source-code
- Close to the core Firefox feel
- Telemetry stripped out and honed for privacy
- Compatible with Firefox extensions
- Receives less frequent security updates than Firefox
An alternative to optimizing your Firefox browser’s settings is to use a ‘Firefox fork’ — a browser separated from Firefox’s open-source code at some point in its development history.
LibreWolf is a community-maintained Firefox fork available for Windows, macOS, and Linux. The browser’s primary focus is privacy, security, and user freedom.
LibreWolf is pre-configured to protect against tracking, browser fingerprinting, and data collection, which makes it a great choice if you don’t want to change Firefox’s settings yourself.
LibreWolf uses DuckDuckGo as the default search engine, collects no telemetry, filters content, and blocks ads using uBlock Origin.
LibreWolf is always based on the latest version of Firefox, but it’s a separate browser from Firefox and does not have auto-update capabilities.
If there’s an urgent Firefox security patch, it will only be released on LibreWolf a few days after, and you will have to manually update the app. This means it isn’t always as secure as Firefox itself.
4. GNU IceCat: Built Entirely from ‘Free Software’
![]()
- Based on Firefox source-code
- Built from free software
- Optimized for privacy
- Sacrifices performance
- Only available for Linux
Built on the principle of ‘free software’, IceCat is a part of a full rework of the Mozilla suite which prioritizes privacy and transparency.
Because of its commitment to free software, IceCat is only available for Linux. This means it isn’t an option for Windows or macOS users.
IceCat has been developed based on an ethical commitment to making and using software which is free for anyone to inspect, edit, and reproduce, even at the expense of utility.
It comes with several add-ons designed to maximize your privacy, including HTTPS Everywhere, SpyBlock and Fingerprinting Countermeasures. These ensure your connection to websites is secure whenever possible, and prevents third-party tracking and even fingerprinting.
IceCat also comes with LibreJS, an add-on designed to prevent proprietary javascript from running in your browser and extracting data without permission.
Because IceCat is not just Open Source but also free, you can inspect all elements of its code and even modify it to suit your preferences. You can also be sure that all future versions or variants of the browser keep the same commitment to transparency.
5. The Tor Browser: Fully Anonymous Browser

- Grants access to the anonymous Tor Network
- Requires some technical knowledge to use properly
- Built on Firefox
- Much slower than alternatives
- Not effective for torrenting or streaming
The Tor browser is a modified version of Firefox which grants you access to the Tor Network and comes optimized for your privacy and anonymity.
The Tor network has some similarities to a VPN. Unlike a VPN, however, it is decentralized — so you never have to trust a private company with your data.
If you aren’t careful with Tor, you can risk undermining your anonymity and leaving yourself vulnerable to direct criminal or government surveillance.
For an added layer of encryption, you can combine Tor with a VPN to improve your safety on Tor. If you connect to a VPN server before connecting to Tor, this is known as Onion over VPN.
In addition, the Tor network can be quite a bit slower than using a simpler privacy-focused browser.
When used correctly, Tor is one of the best tools for online anonymity. That said, it does come with some major drawbacks. We recommend doing some research about Tor and how it compares to VPN services, so you can make sure it’s the best tool for your privacy needs.
How to Stay Anonymous When Using Tor
Using Tor correctly isn’t difficult, but it isn’t always intuitive. It has two big weaknesses:
- A tendency to leak identifiable information when not used properly.
- Public exit nodes which may allow strangers to eavesdrop on your traffic.
To maintain your anonymity, follow these basic steps:
- Never log in to social media or email accounts that are associated with your internet use outside of Tor.
- Don’t post details about your real-life identity.
- Always use secure HTTPS sites.
- Don’t use mobile two-step verification.
- Never torrent on the Tor Browser. This risks IP address leaks, but also drastically slows the network for everyone involved.
- Stay away from Google (alternatives include DuckDuckGo, Searx.me, Qwant, and Start Page).
If you’re extremely privacy conscious it is also recommended that you avoid full-screen. When your browser window is fullscreen it can reveal information like your screen resolution and size, which distinguishes your session from other Tor users and can help with browser fingerprinting.
6. Brave Browser: An Alternative Approach to Advertising

- Reimagines online advertising
- Built on Chromium
- Completely free and open-source
- Includes anti-tracking technology
- Not the most private browser available
Built by the developer of JavaScript after he left Mozilla, Brave is a privacy-focused browser that aims to rework traditional online advertising.
Normal adverts and trackers are blocked by default. Instead, Brave shows its own advertisements and rewards users with its own native cryptocurrency called BAT. If you want to claim these rewards you will need to supply an email address.
These adverts are customized based on your browsing history, which is stored locally in the browser, not sent back to Brave. For true privacy enthusiasts, even this local storage may overstep the mark.
The Brave Browser can also be optimized for blocking ads on the Twitch platform.
The Brave browser also has its own customizable “shields” system, which allows the user to quickly toggle security and privacy measures such as script blocking, device recognition blocking and cross-site cookie blocking.
Brave is free and open-source, which is encouraging from a transparency perspective. You can see the source code on Github.
Brave isn’t without controversy though. The browser’s foundation is in Google Chromium — the open-source project behind the Google Chrome browser and Google Chrome OS. This is a point of anxiety for many users.
Being based on Chromium comes with some privacy downsides. It isn’t possible to disable WebRTC, for instance. While Chromium is open-source now, there is no guarantee it will continue to be in the future.
Unlike most of the other browsers on this list it is also produced by a company looking to make money from advertising, not a group of volunteer privacy enthusiasts. Brave automatically pockets 15% of the revenue from its ads. We’ll let you decide whether this undermines the project or not.
Brave collects some anonymized information about its users, and this cannot be turned off. It claims this information isn’t telemetry, but the lack of user control is concerning from a privacy perspective.
If you buy into its vision for advertising and trust the company to deliver on it, Brave could be a good choice. However, there are better options if privacy is your main point of concern.
How to Optimize Brave for Privacy
Brave can be a secure, privacy-focused browser if you avoid its advertising arm. Even if configured properly, it is still not as effective as browsers based on Firefox.
Stay away from the BAT reward feature if you’re concerned about privacy. It’s turned off by default and we recommend you keep it that way.
If you’ve already turned on the rewards system, it’s easy to turn off by clicking the triangular ‘rewards’ button in the top right hand corner of the browser.

How to disable Brave’s rewards feature.
7. ‘Ungoogled’ Chromium: the Closest Option to Google Chrome

- Built on Chromium, which is open-source
- All connections to Google removed
- Very similar feel to Chrome
- Compatible with Chrome add-ons
- Semi-frequent security updates
Ungoogled Chromium is exactly what it sounds like: Google Chrome with every possible bit of Google taken out or turned off.
The Chromium Projects are the open-source projects behind the Google Chrome browser and Google Chrome OS. While they are open-source, they are still made by Google.
Chromium browsers send information back to Google by default. Even with ‘Ungoogled’ Chromium, it is hard to confirm that this feature has been turned off completely.
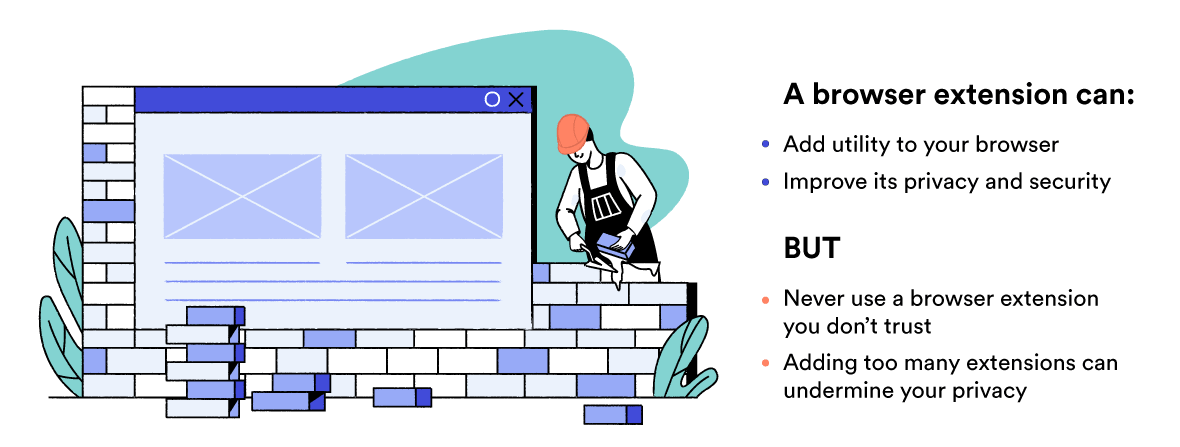
Ungoogled Chromium gives you access to add-ons designed for Chrome. While this is useful, it’s worth remembering that more add-ons make your browser easier to identify. In addition, every add-on you install is a potential way for Google and other third parties to collect your data.
In short, only use add-ons you completely trust. You can learn more about browser add-ons and extensions later in this guide.
There are also other Chromium based browsers to consider including Iridium. Iridium has a similar set of goals to Ungoogled Chromium, but is generally updated less frequently.