The best way to block browser fingerprinting is to use a private browser that restricts it. There are also plug-ins that you can add to mainstream browsers to block some fingerprinting techniques.
Privacy-Focused Browsers
Some browsers do more to block fingerprinting than others, so it’s worth considering your browser choice.
The Tor Browser
The Tor browser is designed for privacy, with its own network of server nodes that enhance your anonymity.
Tor’s strategy is to ensure all users have the same fingerprint, so they can’t be told apart.
Tor has extensive countermeasures to fight browser fingerprinting. These include:
- Disabling all plug-ins.
- Requiring permission for the canvas feature to be used correctly. Otherwise, a pure white image is drawn.
- Ensuring WebGL does not run unless authorized by the user.
- Providing a set of fonts and hiding the installed fonts on the device.
- Setting the browser window to a multiple of 200×100 pixels, and a maximum of 1000×1000 pixels.
- Disabling access to connected media devices like cameras and microphones.
- Disabling the battery status features.
- Delivering the same time zone for everyone
- Disabling the WebAudio API used for audio fingerprinting.
Although everyone’s fingerprint is the same using Tor, it’s not always safe. The use of Tor itself can be detected, and it might be flagged as suspicious and blocked by some services.
Firefox
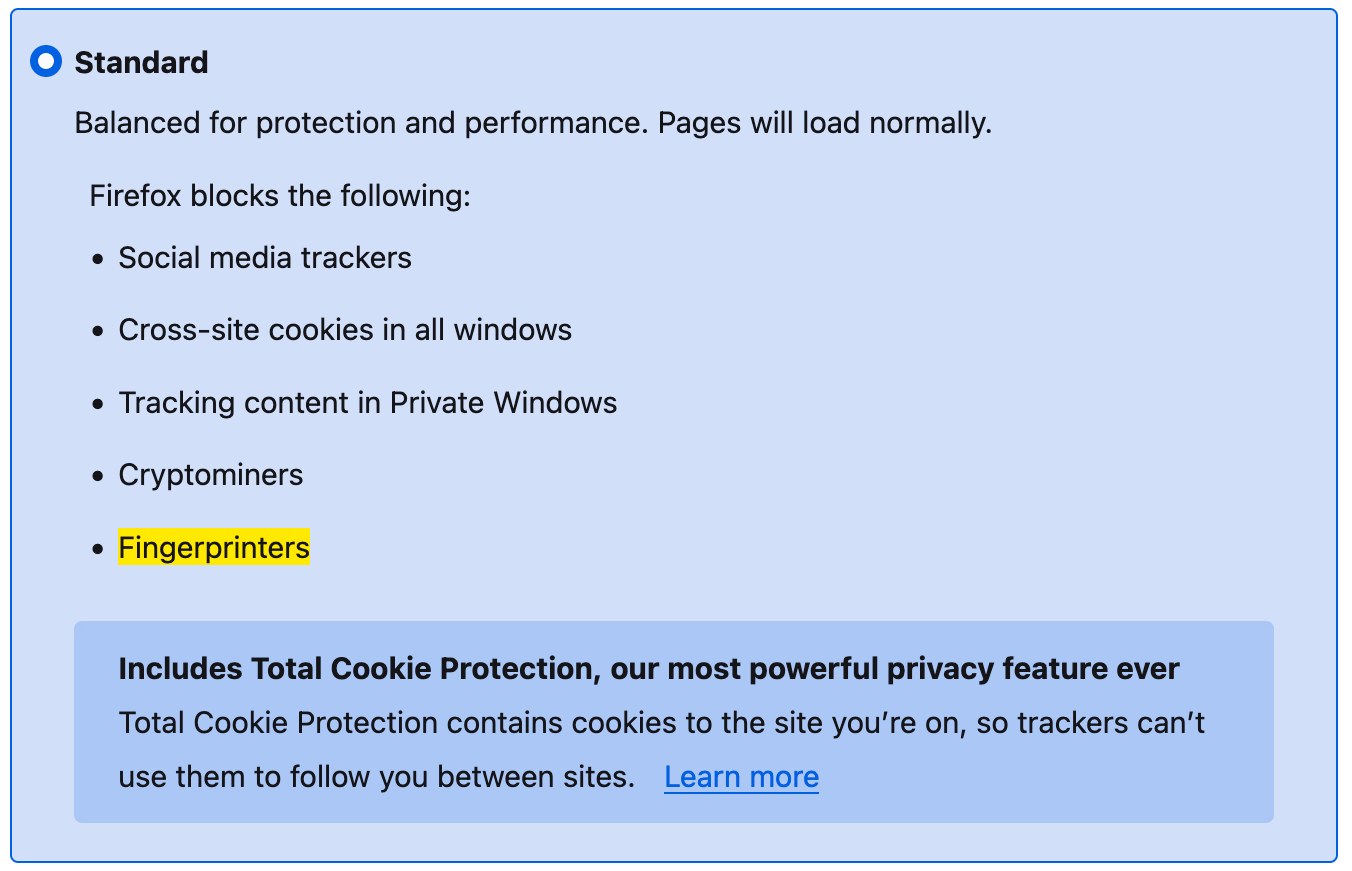
The Firefox browser claims to include fingerprinting protection. It blocks requests from companies that it knows use fingerprinting technologies.
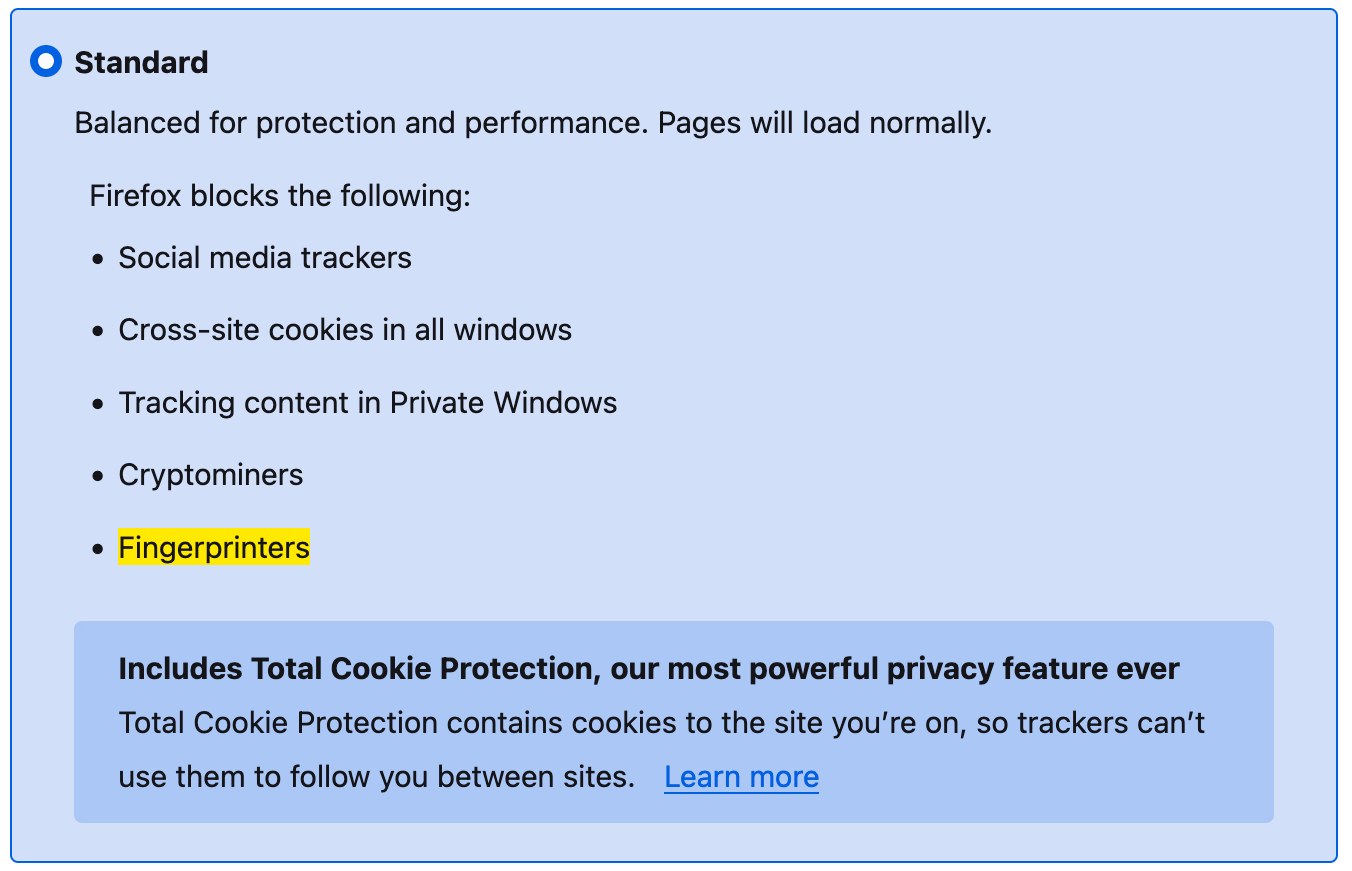
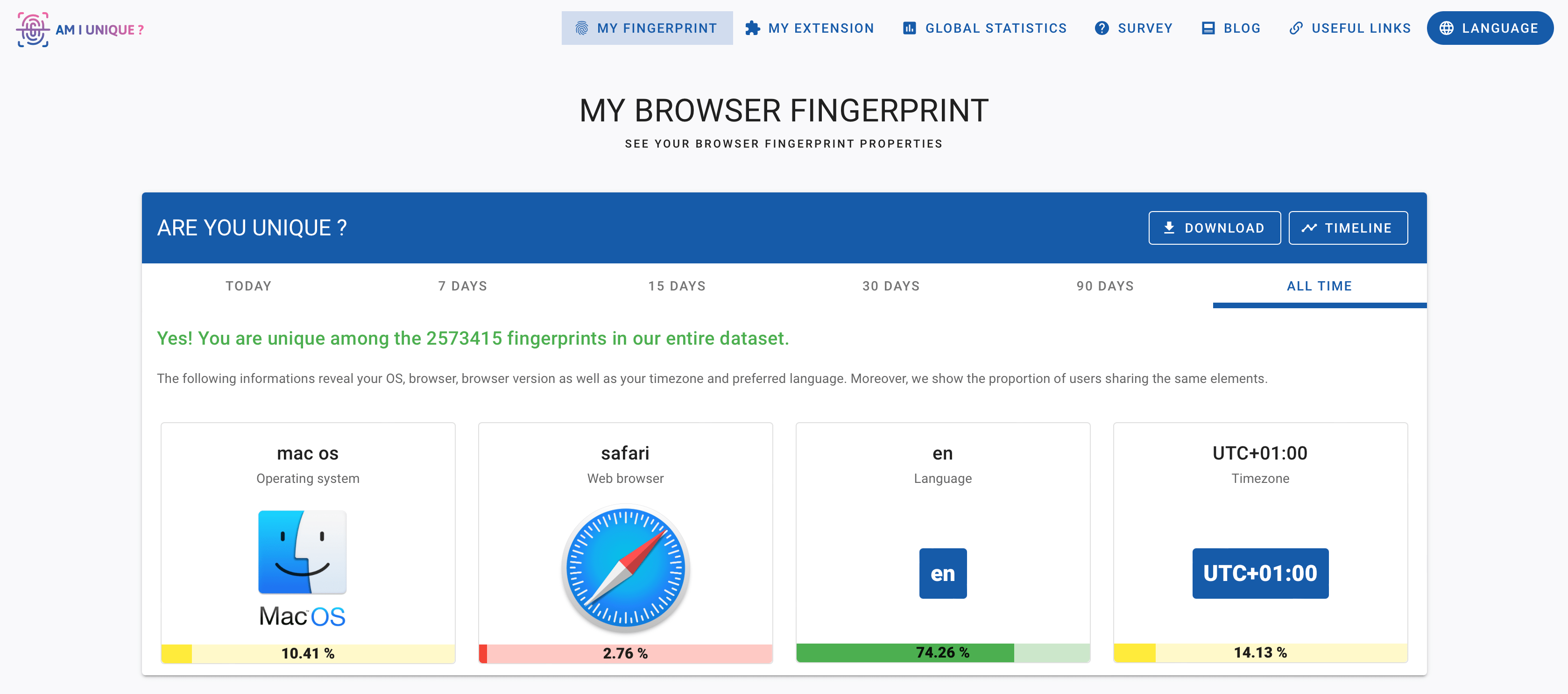
However, we ran Firefox through AmIUnique and found that our browser fingerprint was still unique. It’s possible that the fingerprinting tool we used is not on Firefox’s list of blocked sites, and that it still offers protection against other genuine privacy threats.
EXPERT TIP: LibreWolf is a version of Firefox with additional privacy settings enabled. However, it is updated less often, which arguably weakens its security. IceCat for Linux is another version of Firefox with additional fingerprinting countermeasures.
Avast Secure Browser
Avast Secure Browser claims to confuse fingerprinting scripts to stop them collecting accurate information. Avast says that its browser uses a combination of generalization (so you look like others) and randomization (so your fingerprint changes often).
Our tests found that our fingerprint was still unique while using Avast Secure Browser. As with Firefox, it might perform better with some real tracking scripts, but the browser itself is highly distinctive because it’s used by so few people.
Avast AntiTrack is a commercial product (from $55 per year) that gives fingerprinting scripts fake data, so they can keep running but your real information is hidden.
Brave
The Brave browser replaces adverts and trackers with its own adverts based on your locally stored browsing history.
Brave aims to randomize fingerprint data, so that you have a consistent fingerprint within a browser session on a specific website but have a different fingerprint in other sessions or on other websites. This renders fingerprinting useless for tracking users across sites or site visits.
The developers say this is a better approach than giving everyone the same fingerprint, because some websites will break if fed inaccurate information and your browser might still look unique if a site doesn’t have many visitors like you.
Brave uses the term “farbling” to refer to slightly randomizing the output of browser features that might help to identify you. The browser applies farbling to canvas, media devices, WebGL, plug-ins, audio, and the user agent.
Browser Privacy Settings
We recommend avoiding Microsoft Edge, Chrome, and Safari if you’re really concerned about privacy.
However, if you must use them, there are some features you can enable to limit browser fingerprinting.
Enabling Fingerprint Protection in Safari
Apple’s fingerprint protection in the Safari browser blocks known fingerprinters on pages you visit. It’s enabled by default in private browsing windows, but you can turn it on for all browsing sessions:
- Go to Settings > Safari > Advanced.
- Select Advanced Tracking and Fingerprinting Protection.
- Select All Browsing.
Enabling Fingerprint Protection in Microsoft Edge
Microsoft Edge aims to detect and block fingerprinting trackers. You can enable tracking prevention in Settings > Privacy, search, and services.
There are three levels:
- Basic blocks harmful trackers but allows trackers for ads and content personalization.
- Balanced blocks harmful trackers and third-party trackers from sites you haven’t visited.
- Strict blocks most trackers across websites. Some website features might not work correctly, but you can add exceptions for any sites you want to be excluded from tracking protection.
Browser Extensions
There are several extensions that help to restrict browser fingerprinting. They either block the fingerprinting technology or prohibit known fingerprinters from tracking you.
| Browser Extension |
What It Blocks |
| Canvas Blocker |
Canvas, WebGL, audio, navigator properties, screen, and others. |
| Ghostery |
Known fingerprinters and requests from unknown trackers. |
| Privacy Badger |
Canvas fingerprinting used by advertisers and other third-parties. |
| NoScript |
JavaScript, except where you allow it. |
| Canvas Fingerprint Defender |
Canvas fingerprinting attempts by adding random data to images. |
| Disconnect |
Known third-party browser fingerprinters. |
It’s worth reiterating that these extensions do not offer complete protection against browser fingerprinting. Here’s a summary of what can be protected, and what may still be vulnerable:
| Can Be Protected |
Not Always Protected |
| Companies known to track users |
First-party tracking i.e. fingerprinting by a website you have chosen to visit |
| The most invasive fingerprinting techniques |
Every parameter that can be used to generate a fingerprint |
|
Unknown organizations engaging in fingerprinting |
For the most comprehensive protection, we recommend using two extensions together:
- Canvas Blocker, to block the biggest fingerprinting techniques
- Ghostery, to block known fingerprinting companies
You can find these extensions in your browser’s extension store. Alternatively, visit their website, where they have one, linked in the table above.
VPNs and Proxy Servers
Your IP address is almost certainly unique and can be used to identify you. It makes sense, then, to use a VPN or proxy server to change your IP address, and to gain the other privacy and security benefits of using a VPN.
If you change your VPN server, you’ll partly change any fingerprint that uses your previous IP address.
However, a VPN will do nothing to prevent other fingerprinting techniques being used against you. It doesn’t stop the browser from revealing information about your graphics card, screen, or connected media devices, for example.