China’s Surveillance State: A Global Project

Researchers Valentin Weber and Vasilis Ververis reveal the global reach of Huawei’s surveillance tools and uncover the U.S. companies that facilitate China’s surveillance state.
Key Research Findings
Huawei’s Global Reach
- 1,799 surveillance devices are active in 69 countries, including in Xinjiang, China.
- Their technology is being used to block websites in at least 17 countries.
- 13 controversial ‘Safe Cities’ are in operation, including in Lahore, Islamabad, and Nairobi.
Chinese Tech Firms Abroad
- 14 Chinese companies with links to China’s state surveillance project, the Golden Shield, continue to operate internationally.
- 10 companies continue to have commercial relationships with U.S. firms
U.S. Companies in China
- Technology made by seven American companies, including IBM, Microsoft and Oracle, continues to facilitate China’s surveillance state.
- Intel core processors are “likely being used for surveillance purposes” in Xinjiang.
About the Authors
Valentin Weber is a DPhil Candidate in Cyber Security and International Relations at the Centre for Doctoral Training in Cyber Security, University of Oxford. Previously, he was an Open Technology Fund Senior Fellow in Information Controls at the Berkman Klein Center for Internet & Society, Harvard University.
Vasilis Ververis is a PhD candidate at the Humboldt University of Berlin, researching the technical implementations of internet censorship and surveillance. His latest project is the magma guide, an open-licensed, collaborative guide on information controls and internet censorship.
Introduction
A new report supported by Top10VPN’s Digital Rights Research Grant reveals the global proliferation of Huawei’s surveillance technology and the U.S. companies whose products continue to be used by Chinese police departments.
The findings show that despite efforts to decouple the two countries’ tech sectors, American products continue to play a vital role in China’s digital surveillance program, the Golden Shield.
The report also demonstrates that despite increased international pressure, Chinese companies, including Huawei, continue to enjoy lucrative international commercial opportunities.
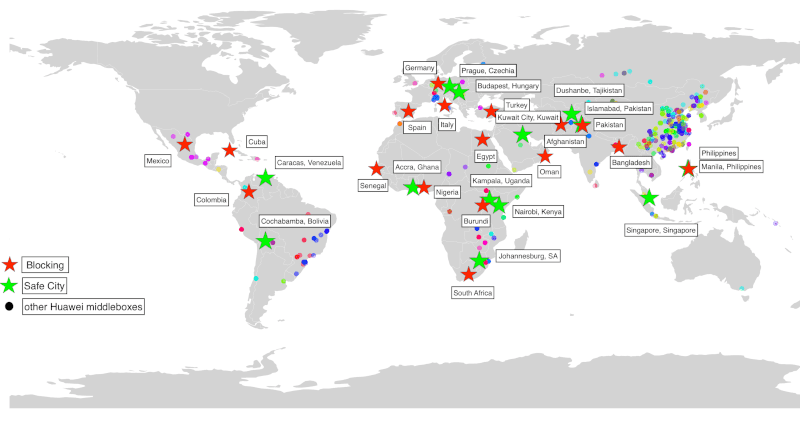
The researchers identified almost 2,000 Huawei middleboxes in 69 countries via network measurement analysis. The products are capable of monitoring people’s internet activity and blocking access to certain websites.
In 17 countries, Huawei middleboxes were found to be blocking content, including an LGBTQI+ website in Oman and a domestic radio station in Burundi.
Products made by at least seven U.S. companies continue to be used by Chinese state actors, including Intel core processors which are “likely being used for surveillance purposes” in Xinjiang.
Meanwhile, at least 14 Chinese companies involved in China’s Golden Shield Project continue to operate internationally. Beijing Zhongke Fuxing Information Technology Co Ltd., for example, has completed several surveillance-related projects in Xinjiang. Despite this, Microsoft, IBM, Intel, HP, and Oracle are still listed as their commercial partners.[1]
The researchers note that unless the Chinese Communist Party (CCP) has secretly ordered companies to remove the backdoors that must be built into their software domestically, some of these exports could be used to access and monitor the data of people internationally.
As pressure on the CCP continues to rise, this research sheds light on the companies that continue to play a role in the construction of China’s surveillance state. It also shows that despite this pressure, Chinese tech firms implicated in domestic surveillance continue to enjoy lucrative commercial partnerships abroad.
Download the full report, China’s Surveillance State: A Global Project
Huawei's Global Reach
Middleboxes can be used for a variety of purposes, from network security to traffic optimization. They also allow ISPs and businesses to monitor web traffic, block websites, and even distribute malware.
As the researchers note: “Middleboxes can be found in most networks across the world since they are deployed by most ISPs. Their worldwide dissemination and access to sensitive information means that they are crucial to the national security of any country.”
Our previous research has shown how surveillance middleboxes equipped with deep packet inspection may have facilitated social media shutdowns around the world.
A huge amount of sensitive information passes through middleboxes. As such, UK intelligence agencies recently warned that Chinese-made middleboxes and other ‘safe city’ technologies could pose a risk to national security.[2]
Despite this, 1,799 Huawei-made surveillance middleboxes were identified in 69 countries.
This includes two middleboxes in central Urumqi and one in Turpan, both areas of Xinjiang where mass surveillance is said to have supported the ongoing repression of Uyghurs.
In the following 17 countries, the technology is being used to censor content:
- Afghanistan
- Bangladesh
- Burundi
- Colombia
- Cuba
- Egypt
- Germany
- Italy
- Mexico
- Nigeria
- Oman
- Pakistan
- Paraguay
- Senegal
- South Africa
- Spain
- Turkey
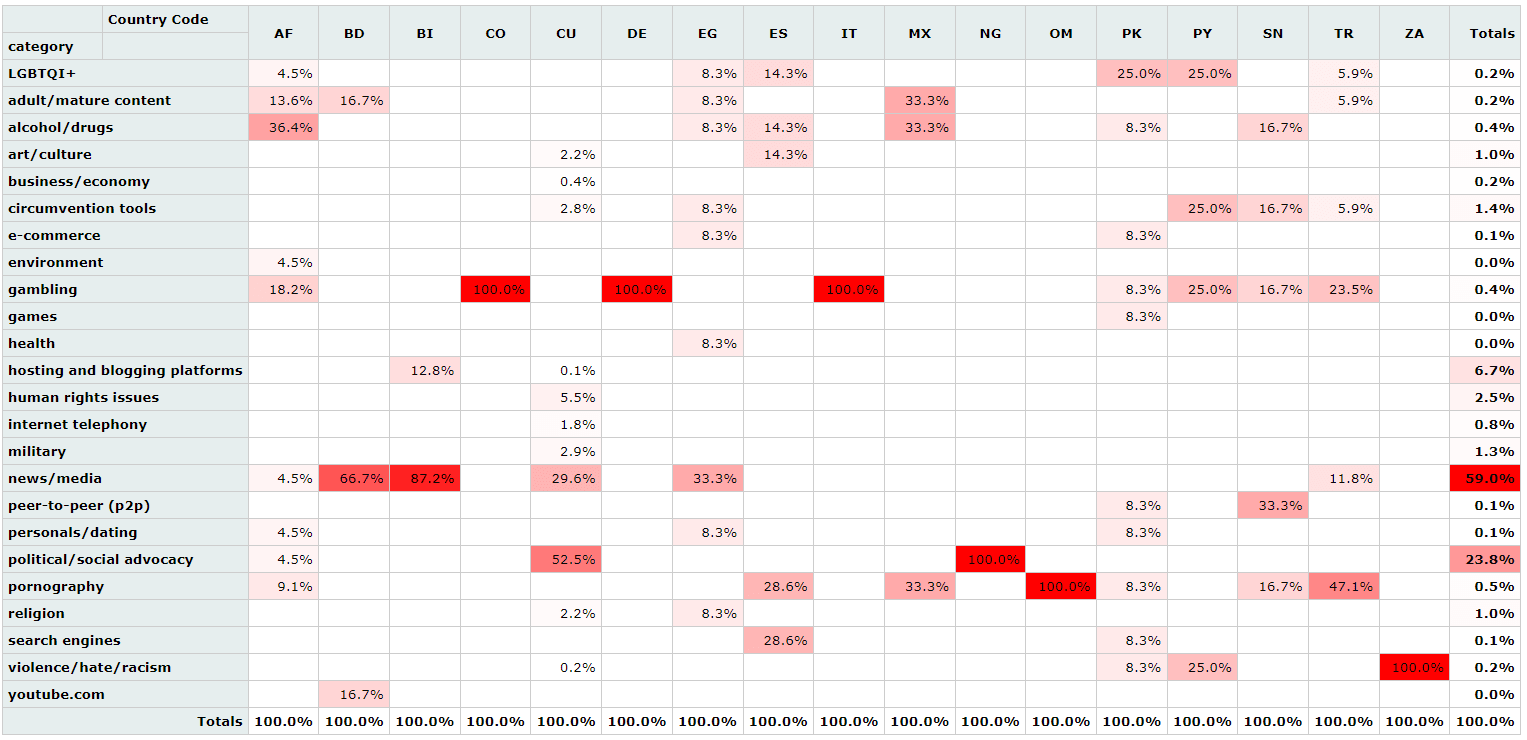
The type of content blocked by Huawei’s technology varies by country.
In six countries, news and media websites are blocked, including in Afghanistan, Cuba and Egypt. In Pakistan, Paraguay, Turkey, Oman, and Spain, LGBTQIA+ websites are currently being blocked. In Nigeria, Cuba, and Afghanistan, Huawei’s technology is being used to restrict access to political and social advocacy websites.
The findings demonstrate that Huawei’s technology continues to be used to censor content internationally and may represent growing international acceptance of the CCP’s highly restrictive approach to information controls.
While this content is blocked on specific AS networks — a network of connected devices normally operated by a single organizations such as as an ISP or large business — the findings do not show with absolute certainty that those websites are subject to country-wide blocking.
To access content blocked on a specific AS network, censorship circumvention technologies, such as personal VPN services, can be used.
Huawei’s middleboxes are not only being used to restrict access to certain content. Through cross-referencing the location of middleboxes and known safe city projects, the report identifies at least 13 safe cities that are, at the very least, semi-operational.
- Accra, Ghana
- Budapest, Hungary
- Caracas, Venezuela
- Cochabamba, Bolivia
- Dushanbe, Tajikistan
- Islamabad, Pakistan
- Johannesburg, South Africa
- Kampala, Uganda
- Kuwait City, Kuwait
- Manila, Philippines
- Nairobi, Kenya
- Prague, Czechia
- Singapore
Safe cities are one of Huawei’s main public safety solutions and use a network of Internet of Things (IoT) devices to help advance policing efforts. They also represent a central aspect of the current phase of China’s Golden Shield Project.
However, digital privacy activists have long warned of their potential to spur an increase in surveillance in ways that may harm human rights.
“Huawei’s Safe City initiative undoubtedly threatens human rights in Uganda, including the right to peaceful assembly and association” – Dorothy Mukasa, Unwanted Witness[3]
Information regarding safe cities is scarce. While there is an abundance of marketing material about the projects, there are rarely detailed updates from government agencies regarding their development.
These findings show that these projects are at least semi-operational and that Huawei’s technology is already active.
China's Tech Firms Abroad
The report also reveals that Chinese companies that play a part in the Golden Shield Project continue to enjoy potentially lucrative international commercial opportunities.
Neusoft’s population management product processes fingerprint, facial recognition and household registration data. It has been deployed in Xinjiang.[4] PwC has listed Neusoft as one of the ‘Global 100 Software Leaders’ four times and the company continues to collaborate with Intel on network technology.[5]
Like many of the companies referenced in the report, Neusoft not only benefits from relationships with U.S. companies. They also have shareholders based in Japan and Europe.[6]
Feitian creates two-factor authentication and smart-card-based products and is based in Beijing. It has supplied the national police and potentially the People’s Liberation Army (PLA) with USB keys.[7] It has also supplied Google with security keys for the U.S. company’s Advanced Protection Program. [8]
Dragon Information Technology is a prominent manufacturer of public security intelligence platforms. In 2017, it signed an agreement with the Tibet Autonomous Region Public Security Department to establish a big data and cloud computing product that would encourage a “safe Tibet” and create a “stable social atmosphere”.[9] Its international partners include Microsoft, Oracle, Dell, IBM and Cisco.[10]
The following table shows full details of the Chinese companies referenced in the report and their involvement with international companies.
U.S. Companies & China's Surveillance State
The report shows that American companies including Microsoft, Oracle, Dell, and Cisco “supply vital equipment to Chinese police departments across the country”.
While some of the deals may have been completed via subsidiaries and third parties, the findings reveal that U.S. products are still being used to facilitate China’s surveillance state.
Intel core processors are included in a 2020 procurement document published by the Government Procurement of Xinjiang.[11] It shows the Diwopu International Airport Branch of the Public Security Bureau of Urumqi City, Xinjiang, purchased electronic equipment in 2020 for ¥205,000 (around $1,800). According to the authors of the report: “The Diwopu airport police is crucial to control in Xinjiang. It monitors one of the few international routes into and out of Xinjiang.”
In Fujian Province, a procurement document shows the use of Oracle, Microsoft and IBM products to power the Fuzhou Public Security Bureau and Zhongshan Public Security’s Public Security Cloud Platform Project.[12] The document shows that American products will be used to support a platform that handles facial recognition, big data policing, and license plate recognition data.
In Beijing, a bidding document reveals that the Beijing Municpal Public Security Bureau uses IBM servers, Oracle Database 10g, and Cisco Netflow cards.[13] While it is likely the products are being used to improve network security, the Beijing police department has previously been accused of detaining a human rights lawyer and arresting citizens for archiving digital content relating to COVID-19.[14][15]
The following table shows full details of U.S. companies referenced in the report and their links to China’s surveillance project, the Golden Shield.
About Top10VPN's Digital Rights Research Grant
Top10VPN’s Digital Rights Research Grant program provides a platform for researchers, postgraduate students and civil society organizations to conduct primary research on a wide range of critical digital rights issues. It will culminate in a research paper initially hosted on our website.
Main image: Chinese flags next to security warning posted in square of Grand Bazaar with minarets of mosque against blue skies in Urumchi, Xinjiang Autonomous Region, China. Credit: karenfoleyphotography / Alamy
Updated Aug 17 to adjust Huawei middlebox findings throughout to remove Bulgaria after a small number of geolocation measurement errors in underlying OONI data were identified. These amendments were also applied to the full report, along with correction of minor typos in the “List of blocked websites section” and the addition of a clarifying note in the “OONI data” section.
Updated Aug 12 to correct a minor typo in the Heatmap image in the section titled Huawei’s Global Reach. The same correction was also made to the full report.
References
[1] https://web.archive.org/web/20210522081045/http:/sinobeststar.com/page/7.html↩
[2] https://www.ft.com/content/47c9b28b-8247-4984-9398-dc78ff62b424↩
[3] https://qz.com/africa/1822312/huaweis-surveillance-tech-in-africa-worries-activists/↩
[4] https://www.neusoft.com/cn/industries/2126/↩
[5] https://web.archive.org/web/20210518145603/https:/networkbuilders.intel.com/ecosystem/neusoft/ ↩
[6] https://web.archive.org/web/20210310073924/https:/www.neusoft.com/Investor/2407/↩
[7] https://web.archive.org/web/20210520131352/http:/oa.zycg.cn/article/wsjj_show/202028?newdays=5&title=北京国富安电子商务安全认证有限公司USB-Key采购项目(GDC-20131104155902028)需求公告↩
[8] https://www.ftsafe.com/article/621.html↩
[9] https://web.archive.org/web/20210524073951/http:/dragoninfo.com.cn/article_detail.php?id=1505↩
[10] https://archive.fo/cZOj9↩
[11] https://web.archive.org/web/20210430092108/http:/www.ccgp-xinjiang.gov.cn/ZcyAnnouncement/ZcyAnnouncement4/ZcyAnnouncement3004/UsRwZaKmXQXxl/+QSbkPTw==.html↩
[12] https://web.archive.org/web/20210429093321/http:/www.ccgp-fujian.gov.cn/3500/notice/d03180adb4de41acbb063875889f9af1/A4F22F272A835983E053C454A8C07986/↩
[13] https://web.archive.org/web/20210511130818/http:/103.83.45.82/api/placardPreview?bidId=098e06ff2700499d93f80c1147f39420↩
[14] https://www.hrw.org/world-report/2019/country-chapters/china-and-tibet↩
[15] https://www.hrw.org/world-report/2021/country-chapters/china-and-tibet↩